ISO/IEC TR 6114:2023
Cybersecurity - Security considerations throughout the product life cycle
This document describes security considerations throughout the product life cycle (SCLC), which is a framework that spans the entire information and communications technology (ICT) product life cycle. The aim of the framework is to align the industry and bring greater transparency to customers at every point on the ICT product life cycle.This document describes the following items for suppliers, end users (consumers), intermediaries of the ICT supply chain, service providers, and regulators:— definition of phases in the ICT product life cycle from concept to retirement;— threat vectors possible in each phase of the life cycle;— potential controls against those threat vectors.The target audiences of this document are suppliers and consumers of ICT products, including all participants throughout the supply chain such as silicon chip designers, fabricators, product assemblers, logistics providers, service providers, and information security organizations. Clauses 5 to 11 target an organization’s strategic and risk management teams. This document provides an end-to-end view of the threats in each phase to help the organization shape their plans, procedures and policies.
This document describes security considerations throughout the product life cycle (SCLC), which is a framework that spans the entire information and communications technology (ICT) product life cycle. The aim of the framework is to align the industry and bring greater transparency to customers at every point on the ICT product life cycle.
This document describes the following items for suppliers, end users (consumers), intermediaries of the ICT supply chain, service providers, and regulators:
— definition of phases in the ICT product life cycle from concept to retirement;
— threat vectors possible in each phase of the life cycle;
— potential controls against those threat vectors.
The target audiences of this document are suppliers and consumers of ICT products, including all participants throughout the supply chain such as silicon chip designers, fabricators, product assemblers, logistics providers, service providers, and information security organizations. Clauses 5 to 11 target an organization’s strategic and risk management teams. This document provides an end-to-end view of the threats in each phase to help the organization shape their plans, procedures and policies.
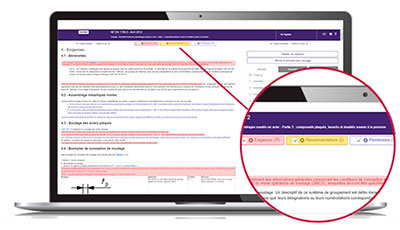
The Requirements department helps you quickly locate within the normative text:
- mandatory clauses to satisfy,
- non-essential but useful clauses to know, such as permissions and recommendations.
The identification of these types of clauses is based on the document “ISO / IEC Directives, Part 2 - Principles and rules of structure and drafting of ISO documents ”as well as on a constantly enriched list of verbal forms.
With Requirements, quickly access the main part of the normative text!
COBAZ is the simple and effective solution to meet the normative needs related to your activity, in France and abroad.
Available by subscription, CObaz is THE modular solution to compose according to your needs today and tomorrow. Quickly discover CObaz!
Request your free, no-obligation live demo
I discover COBAZ